Active Directory Service Account
The Active Directory Service Account setup sequence is necessary only if PKI is a chosen authentication method.
For organizations choosing not to incorporate PKI as an authentication method, this configuration sequence can be skipped completely.
AD Service Account Configuration
Follow these steps to create the Active Directory Service Account in RapidIdentity Server.
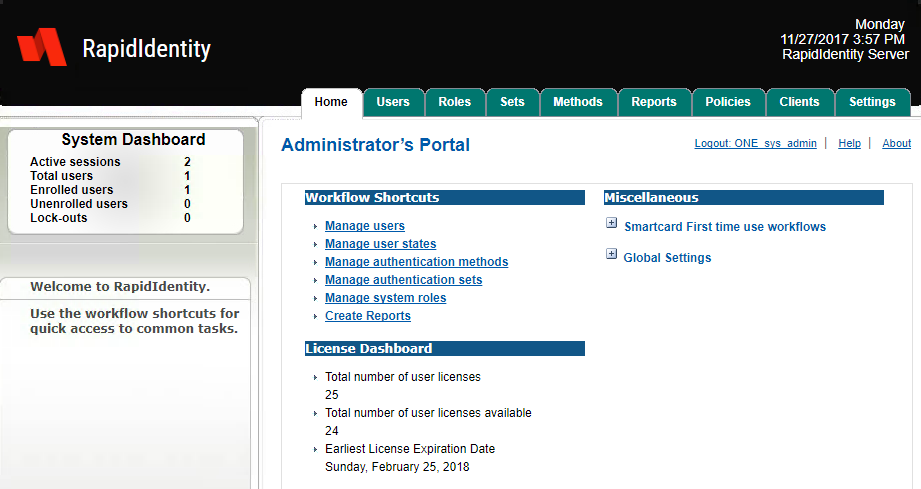
Authenticate to RapidIdentity Server and click from the Home screen click Administrator’s Portal.
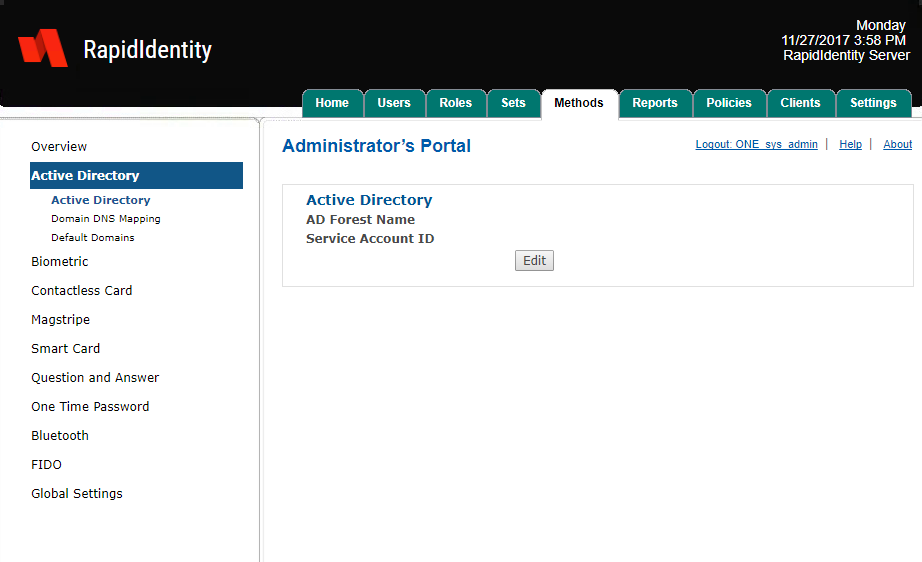
Click Methods and then from the left pane select Active Directory.
Enter the distinguished name of the Active Directory Forest associated with RapidIdentity Server in the AD Forest Name field. In this configuration example, the Forest DN is (DC=MFAServer,DC=local).
Enter the service account user login name in the Service Account ID field and that account’s password in the Active Directory Password field.
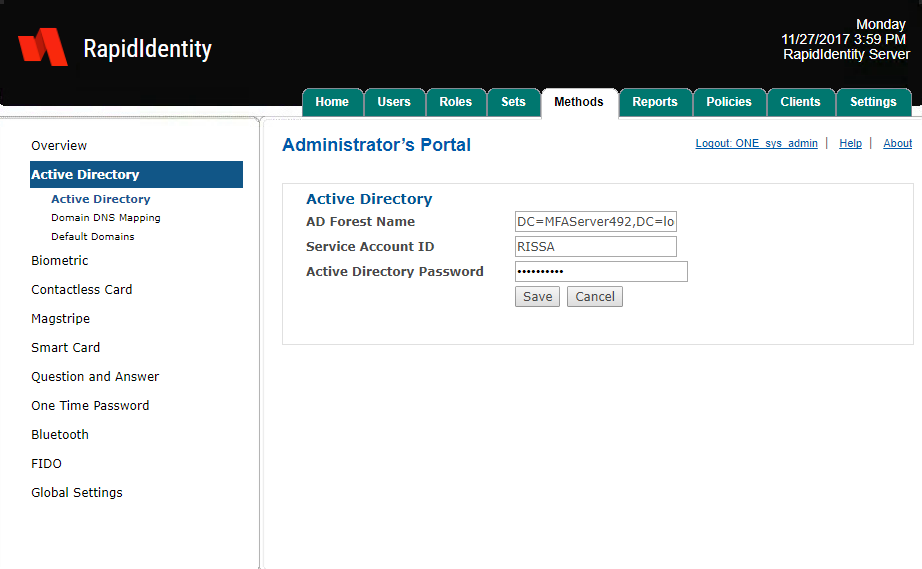
Click Save.
After RapidIdentity Server saves the information the screen will refresh and the option to edit the credentials will be available by clicking Edit.
As a general rule, only the minimum required permissions for the features necessary to use should be assigned to the AD Service Account. In this example, the RISSA account is being used as the Active Directory Service Account. Depending on the features that will be used within RapidIdentity Server, additional permissions are required.
For the majority of the RapidIdentity Server features, only Domain User and Local Admin rights to the computer hosting RapidIdentity Server are required. When publishing the Server URL using AD, Enterprise Admin will be required at the actual time of publishing the URL.
If securing passwords or disabling AD accounts, Domain Admin rights are required.
If using PKI to issue and revoke certificates, various Certificate Authority permissions are be required.
If it becomes necessary to configure any of these permissions, contact Identity Automation Support.